Được xây dựng dựa trên các nguyên tắc cốt lõi của Zero Trust để bảo vệ dữ liệu và truy cập ở mọi nơi, giúp bạn luôn được bảo vệ và làm việc hiệu quả.
Giới thiệu
Việc tăng tốc chuyển đổi kỹ thuật số và mở rộng các nơi làm việc từ xa và kết hợp mang lại cơ hội mới cho các tổ chức, cộng đồng và cá nhân. Kết quả là, phong cách làm việc của chúng tôi đã thay đổi. Và hơn bao giờ hết, nhân viên cần trải nghiệm người dùng đơn giản, trực quan để cộng tác và duy trì năng suất ở bất cứ nơi nào công việc xảy ra. Nhưng việc mở rộng khả năng tiếp cận và khả năng làm việc ở bất cứ đâu cũng đã đưa ra những mối đe dọa và rủi ro mới. Theo dữ liệu mới nhất từ báo cáo Tín hiệu Bảo mật do Microsoft ủy quyền, 75% những người ra quyết định bảo mật ở cấp phó chủ tịch trở lên cảm thấy rằng việc chuyển sang công việc kết hợp khiến tổ chức của họ dễ bị đe dọa hơn trước các mối đe dọa bảo mật.
Tại Microsoft, chúng tôi làm việc chăm chỉ để trao quyền cho mọi người và mọi tổ chức trên hành tinh đạt được nhiều hơn nữa . Chúng tôi cam kết giúp khách hàng an tâm — và luôn tự tin. Với hơn 1 tỷ đô la đầu tư vào bảo mật mỗi năm, hơn 3.500 chuyên gia bảo mật chuyên dụng và khoảng 1,3 tỷ thiết bị Windows 10 được sử dụng trên khắp thế giới, chúng tôi có cái nhìn sâu sắc về các mối đe dọa mà khách hàng của chúng tôi phải đối mặt.
Khách hàng của chúng tôi cần các giải pháp bảo mật hiện đại cung cấp khả năng bảo vệ toàn diện ở bất kỳ đâu. Windows 11 là một bản xây dựng với các nguyên tắc Zero Trust cho kỷ nguyên mới của công việc kết hợp. Zero Trust là một mô hình bảo mật dựa trên tiền đề rằng không người dùng hoặc thiết bị nào ở bất kỳ đâu có thể có quyền truy cập cho đến khi sự an toàn và tính toàn vẹn được chứng minh. Windows 11 nâng cao nền tảng bảo mật với các yêu cầu mới được tích hợp trong cả phần cứng và phần mềm để bảo vệ nâng cao từ chip tới đám mây . Với Windows 11, khách hàng của chúng tôi có thể kích hoạt năng suất kết hợp và trải nghiệm mới mà không ảnh hưởng đến bảo mật.

Khoảng 80% các nhà ra quyết định bảo mật nói rằng một mình phần mềm là không đủ bảo vệ khỏi các mối đe dọa mới nổi. 1
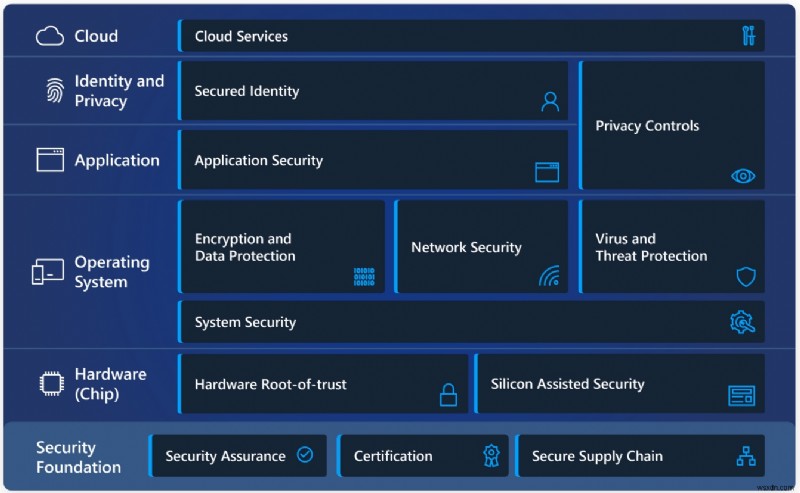
Trong Windows 11, phần cứng và phần mềm hoạt động cùng nhau để bảo vệ từ CPU đến đám mây. Xem các lớp bảo vệ trong sơ đồ đơn giản này và xem tổng quan ngắn gọn về các ưu tiên bảo mật của chúng tôi bên dưới.
Cách Windows 11 kích hoạt tính năng bảo vệ Zero Trust
Các nguyên tắc của Zero Trust có ba nguyên tắc. Đầu tiên, hãy xác minh một cách rõ ràng. Luôn xác thực và ủy quyền dựa trên tất cả các điểm dữ liệu có sẵn, bao gồm danh tính người dùng, vị trí, tình trạng thiết bị, dịch vụ hoặc khối lượng công việc, phân loại dữ liệu và các điểm bất thường. Phương thức thứ hai sử dụng quyền truy cập ít đặc quyền nhất, hạn chế quyền truy cập của người dùng bằng các chính sách thích ứng vừa kịp thời và vừa đủ, dựa trên rủi ro và bảo vệ dữ liệu để giúp bảo mật dữ liệu và năng suất. Và cuối cùng, giả sử vi phạm. Giả định vi phạm hoạt động theo cách giảm thiểu bán kính vụ nổ và khả năng tiếp cận các phân đoạn. Xác minh mã hóa đầu cuối và sử dụng phân tích để có được khả năng hiển thị nhằm cải thiện khả năng phát hiện và phòng thủ mối đe dọa.

Đối với Windows 11, nguyên tắc xác minh Zero Trust áp dụng rõ ràng cho các rủi ro do cả thiết bị và người dùng gây ra. Ngoài ra, windows 11 cung cấp bảo mật từ chip đến đám mây, giúp quản trị viên CNTT chứng thực và đo lường để xác định xem thiết bị có đáp ứng các yêu cầu và có thể đáng tin cậy hay không. Và Windows 11 hoạt động hiệu quả với Microsoft Intune và Azure Active Directory, do đó, các quyết định truy cập và thực thi là liền mạch. Ngoài ra, Quản trị viên CNTT có thể dễ dàng tùy chỉnh Windows 11 để đáp ứng các yêu cầu cụ thể của người dùng và chính sách về quyền truy cập, quyền riêng tư, tuân thủ và hơn thế nữa.
Người dùng cá nhân cũng được hưởng lợi từ các biện pháp bảo vệ mạnh mẽ, bao gồm các tiêu chuẩn mới về bảo mật dựa trên phần cứng và bảo vệ không cần mật khẩu. Giờ đây, tất cả người dùng có thể thay thế mật khẩu tiềm ẩn rủi ro bằng cách cung cấp bằng chứng nhận dạng an toàn với ứng dụng Microsoft Authenticator, đăng nhập bằng khuôn mặt hoặc vân tay, 2 khóa bảo mật hoặc mã xác minh được gửi tới điện thoại hoặc email.
Tổng quan về các ưu tiên bảo mật của Windows 11
Bảo mật, theo mặc định
Gần 90% những người ra quyết định bảo mật được khảo sát nói rằng phần cứng lỗi thời khiến các tổ chức dễ bị tấn công hơn và phần cứng hiện đại hơn sẽ giúp bảo vệ
chống lại các mối đe dọa trong tương lai. Dựa trên những cải tiến của Windows 10, chúng tôi đã làm việc với nhà sản xuất và các đối tác silicon của mình để cung cấp các khả năng bảo mật phần cứng bổ sung nhằm đáp ứng bối cảnh mối đe dọa đang phát triển và cho phép nhiều công việc và học tập kết hợp hơn. Bộ yêu cầu bảo mật phần cứng mới với Windows 11 được thiết kế để xây dựng một nền tảng thậm chí còn mạnh mẽ hơn và có khả năng phục hồi tốt hơn trước các cuộc tấn công.
Bảo mật hệ điều hành và phần cứng nâng cao
Với bảo mật cách ly dựa trên phần cứng bắt đầu từ chip, Windows 11 lưu trữ dữ liệu nhạy cảm đằng sau các hàng rào bảo mật bổ sung, tách biệt khỏi hệ điều hành. Do đó, thông tin bao gồm khóa mã hóa và thông tin đăng nhập của người dùng được bảo vệ khỏi sự truy cập và giả mạo trái phép. Trong Windows 11, phần cứng và phần mềm bảo vệ hệ điều hành, với bảo mật dựa trên ảo hóa (VBS) và Khởi động an toàn được tích hợp sẵn và được bật theo mặc định trên các CPU mới. Ngay cả khi những kẻ xấu xâm nhập, họ cũng không tiến xa được. VBS sử dụng các tính năng ảo hóa phần cứng để tạo và cách ly vùng bộ nhớ an toàn khỏi hệ điều hành. Môi trường cô lập
này lưu trữ nhiều giải pháp bảo mật, giúp tăng cường khả năng bảo vệ khỏi các lỗ hổng trong hệ điều hành và ngăn chặn việc sử dụng các phần mềm khai thác độc hại. Với xác nhận tình trạng của thiết bị bằng các dịch vụ đám mây, Windows 11 đã sẵn sàng cho sự tin cậy.
Kiểm soát quyền riêng tư và bảo mật ứng dụng mạnh mẽ
Để giúp bảo vệ thông tin cá nhân và doanh nghiệp và riêng tư, Windows 11 có nhiều lớp bảo mật ứng dụng để bảo vệ dữ liệu quan trọng và tính toàn vẹn của mã. Tính năng cô lập và kiểm soát ứng dụng, tính toàn vẹn của mã, kiểm soát quyền riêng tư và các nguyên tắc ít đặc quyền nhất cho phép các nhà phát triển tích hợp bảo mật và quyền riêng tư ngay từ đầu. Bảo mật tích hợp này bảo vệ khỏi vi phạm và phần mềm độc hại, giúp giữ dữ liệu riêng tư và cung cấp cho quản trị viên CNTT các quyền kiểm soát cần thiết.
Trong Windows 11, Microsoft Defender Application Guard 3 sử dụng công nghệ ảo hóa Hyper-V để cô lập các trang web không đáng tin cậy và các tệp Microsoft Office trong vùng chứa, tách biệt và không thể truy cập vào hệ điều hành máy chủ cũng như dữ liệu doanh nghiệp. Để bảo vệ quyền riêng tư, Windows 11 cũng cung cấp nhiều quyền kiểm soát hơn đối với các ứng dụng và tính năng có thể thu thập và sử dụng dữ liệu như vị trí thiết bị hoặc truy cập các tài nguyên như máy ảnh và micrô.
Danh tính được bảo mật
Mật khẩu không thuận tiện khi sử dụng và là mục tiêu chính của tội phạm mạng — và chúng đã là một phần quan trọng của bảo mật kỹ thuật số trong nhiều năm. Điều đó thay đổi với tính năng bảo vệ không cần mật khẩu có sẵn trong Windows 11. Sau quy trình ủy quyền an toàn, thông tin đăng nhập được bảo vệ sau các lớp bảo mật phần cứng và phần mềm, cho phép người dùng truy cập an toàn, không cần mật khẩu vào các ứng dụng và dịch vụ đám mây của họ.
Người dùng cá nhân có thể xóa mật khẩu khỏi tài khoản Microsoft của họ và sử dụng ứng dụng Microsoft
Authenticator,
4
Windows Hello,
5
khóa bảo mật FIDO2, thẻ thông minh hoặc mã xác minh được gửi đến điện thoại hoặc email của họ. Quản trị viên CNTT và người tiêu dùng có thể thiết lập thiết bị Windows 11
không cần mật khẩu, tận dụng các công nghệ như Windows Hello phù hợp với tiêu chuẩn Fast Identity Online (FIDO). Windows 11 bảo vệ thông tin xác thực bằng bảo mật phần cứng cấp chip bao gồm TPM 2.0 kết hợp với VBS và Microsoft Credential Guard.
Kết nối với các dịch vụ đám mây
Tính năng bảo mật của Windows 11 mở rộng tính tin cậy không đối với đám mây, cho phép các chính sách, kiểm soát, quy trình và công nghệ hoạt động cùng nhau để bảo vệ thiết bị, dữ liệu, ứng dụng và danh tính của bạn từ mọi nơi. Microsoft cung cấp các dịch vụ đám mây toàn diện để quản lý danh tính, lưu trữ và truy cập cùng với các công cụ để chứng thực rằng bất kỳ thiết bị Windows nào kết nối với mạng của bạn đều đáng tin cậy. Bạn cũng có thể thực thi việc tuân thủ và quyền truy cập có điều kiện bằng dịch vụ quản lý thiết bị hiện đại (MDM) như Microsoft Intune hoạt động với Azure Active Directory để kiểm soát quyền truy cập vào các ứng dụng và dữ liệu thông qua đám mây. 6
Bảo mật phần cứng
Các mối đe dọa hiện đại đòi hỏi bảo mật hiện đại với sự liên kết chặt chẽ giữa bảo mật phần cứng và kỹ thuật bảo mật phần mềm để giữ cho người dùng, dữ liệu và thiết bị được bảo vệ. Chỉ riêng hệ điều hành không thể bảo vệ khỏi nhiều loại công cụ và kỹ thuật mà tội phạm mạng sử dụng để xâm nhập máy tính. Khi vào bên trong, những kẻ xâm nhập có thể khó bị phát hiện trong khi tham gia vào nhiều hoạt động bất chính từ đánh cắp dữ liệu hoặc thông tin đăng nhập quan trọng đến cấy phần mềm độc hại vào phần sụn thiết bị cấp thấp, khó xác định và loại bỏ. Những mối đe dọa mới này đòi hỏi phần cứng máy tính được bảo mật đến tận cốt lõi, bao gồm các chip phần cứng và bộ xử lý lưu trữ thông tin kinh doanh nhạy cảm. Bằng cách xây dựng các khả năng bảo mật trong phần cứng, chúng tôi có thể loại bỏ toàn bộ các lớp lỗ hổng bảo mật mà trước đây chỉ tồn tại trong phần mềm. Điều này cũng thường mang lại hiệu suất đáng kể so với việc triển khai cùng một khả năng bảo mật trong phần mềm, do đó tăng cường bảo mật tổng thể của hệ thống mà không ảnh hưởng đến hiệu suất hệ thống.
Với Windows 11, Microsoft đã nâng cao thanh bảo mật phần cứng để thiết kế phiên bản Windows an toàn nhất từ trước đến nay. Chúng tôi đã lựa chọn cẩn thận các yêu cầu phần cứng và các tính năng bảo mật mặc định dựa trên thông tin về mối đe dọa và thông tin đầu vào từ các chuyên gia hàng đầu trên toàn cầu bao gồm DoD, NSA và NCSC của Vương quốc Anh và nhóm Bảo mật Microsoft của riêng chúng tôi. Chúng tôi đã làm việc với các đối tác sản xuất chip và thiết bị của mình để tích hợp các khả năng bảo mật nâng cao trên phần mềm, chương trình cơ sở và phần cứng nhằm tạo ra sự tích hợp chặt chẽ bảo vệ từ chip tới đám mây.
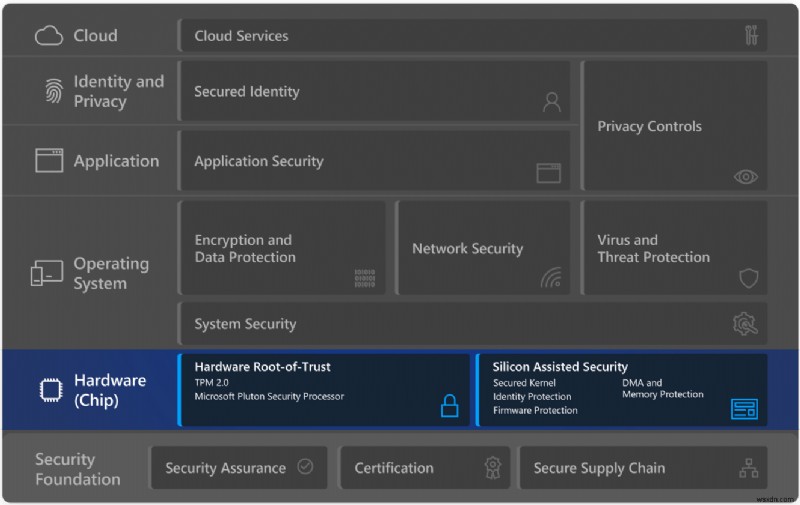
Thông qua sự kết hợp mạnh mẽ giữa sự tin cậy gốc phần cứng và bảo mật được hỗ trợ bởi silicon, Windows 11 mang đến khả năng bảo vệ phần cứng tích hợp sẵn.
Gốc tin cậy phần cứng
Sự tin cậy gốc phần cứng giúp bảo vệ và duy trì tính toàn vẹn của hệ thống khi phần cứng bật, tải phần sụn và sau đó khởi chạy hệ điều hành. Phần cứng rootof-trust đáp ứng hai mục tiêu bảo mật quan trọng cho hệ thống. Nó đo lường an toàn phần sụn và mã hệ điều hành khởi động hệ thống để phần mềm độc hại không thể lây nhiễm mã khởi động và ẩn sự hiện diện của nó. Root-of-Trust phần cứng cũng cung cấp một khu vực bảo mật cao được cách ly với hệ điều hành và các ứng dụng để lưu trữ khóa mật mã, dữ liệu và mã. Tính năng bảo vệ này bảo vệ các tài nguyên quan trọng như ngăn xếp xác thực Windows, mã thông báo đăng nhập một lần, ngăn xếp sinh trắc học Windows Hello và khóa mã hóa số lượng BitLocker.
Mô-đun nền tảng đáng tin cậy (TPM)
TPM được thiết kế để cung cấp các chức năng liên quan đến bảo mật dựa trên phần cứng và giúp ngăn chặn việc giả mạo không mong muốn. TPM cung cấp các lợi ích về bảo mật và quyền riêng tư cho phần cứng hệ thống, chủ sở hữu nền tảng và người dùng. Windows Hello, BitLocker, Windows Defender System Guard và nhiều tính năng khác của Windows dựa vào TPM để tạo khóa, lưu trữ an toàn, mã hóa, đo tính toàn vẹn khởi động, chứng thực và nhiều khả năng khác. Những khả năng này sẽ giúp khách hàng tăng cường bảo vệ danh tính và dữ liệu của họ.
Phiên bản 2.0 của đặc tả TPM bao gồm các cải tiến quan trọng như tính linh hoạt của thuật toán mật mã cho phép các thuật toán tiền điện tử mạnh hơn và khả năng cho khách hàng sử dụng các thuật toán thay thế ưa thích. Bắt đầu với Windows 10, chứng nhận phần cứng của Microsoft yêu cầu tất cả các PC Windows mới phải bao gồm TPM 2.0 được tích hợp sẵn và được bật theo mặc định. Với Windows 11, cả thiết bị mới và thiết bị nâng cấp đều phải có TPM 2.0. Yêu cầu này củng cố vị thế bảo mật trên tất cả các thiết bị Windows 11 và giúp đảm bảo rằng các thiết bị này có thể hưởng lợi từ các khả năng bảo mật trong tương lai phụ thuộc vào root-of-Trust phần cứng.
Tìm hiểu thêm về các thông số kỹ thuật TPM của Windows 11 và cách bật TPM 2.0 trên PC của bạn.
Bộ xử lý bảo mật Pluton
Bộ xử lý bảo mật Microsoft Pluton, cung cấp khả năng bảo mật tại chip. Pluton là phần cứng gốc của sự tin cậy được thiết kế bởi Microsoft với sự hợp tác của các đối tác silicon của chúng tôi nhằm mục đích cung cấp sự mạnh mẽ và linh hoạt cần thiết cho các PC hiện đại để giải quyết các mối đe dọa đang phát triển. Thiết kế Pluton nhúng trực tiếp niềm tin gốc phần cứng vào cùng chất nền silicon với CPU. Nguyên tắc thiết kế quan trọng này giúp loại bỏ một điểm yếu phổ biến khi root-of-Trust nằm trong một chip rời khác trên bo mạch chủ tách biệt với CPU. Điểm yếu là mặc dù bản thân chip root-of-trust có thể rất an toàn, nhưng có một liên kết yếu trong đường giao tiếp giữa root-of-Trust rời rạc và CPU có thể bị khai thác bởi các cuộc tấn công vật lý.
Pluton hỗ trợ tiêu chuẩn công nghiệp TPM 2.0 cho phép khách hàng hưởng lợi ngay lập tức từ tính năng bảo mật nâng cao trong các tính năng của Windows dựa trên TPM bao gồm BitLocker, Windows Hello và Windows Defender System Guard. In addition to being a TPM 2.0, Pluton also supports other security functionality beyond what is possible with the TPM 2.0 specification, and this extensibility allows for additional Pluton firmware and OS features to be delivered over time via Windows Update.
As with other TPMs, credentials, encryption keys, and other sensitive information cannot be extracted from Pluton even if an attacker has installed malware or has complete physical possession of the PC. Storing sensitive data like encryption keys securely within the Pluton processor, which is isolated from the rest of the system, helps ensure that emerging attack techniques such as speculative execution cannot access key material. Pluton also includes the unique Secure Hardware Cryptography Key (SHACK) technology. SHACK helps ensure that keys are never exposed outside the protected hardware, even to the Pluton firmware itself, providing an unprecedented level of security for Windows customers.
Pluton also solves the major security challenge of keeping system firmware up to date across the entire PC ecosystem. Today customers receive updates to their security firmware from a variety of different sources than can be difficult to manage, resulting in widespread update issues. Pluton provides a flexible, updateable platform for running firmware that implements end-to-end security functionality authored, maintained, and updated by Microsoft. Pluton is integrated with the Windows Update service benefitting from over a decade of operational experience reliably delivering updates across over a billion endpoint systems.
The Microsoft Pluton security processor will ship with select new Windows PCs starting in 2022. 7
Silicon assisted security
In addition to a modern hardware root-of-trust, there are numerous other capabilities in the latest CPUs that harden the operating system against threats such as by protecting the boot process, safeguarding the integrity of memory, isolating security sensitive compute logic, and more.
Secured kernel
Virtualization-based security (VBS) , also known as core isolation, is a critical building block in a secure system. VBS uses the CPU’s hardware virtualization instructions to create a secure region of memory isolated from the normal operating system. Windows uses this isolated VBS environment to protect security sensitive operating system functions such as the secure kernel and security assets such as authenticated user credentials. Even if malware gains access to the main OS kernel, VBS greatly limits and contains exploits because the hypervisor and virtualization hardware help prevent the malware from executing code or accessing platform secrets running within the VBS secure environment.
Hypervisor-protected code integrity (HVCI) , also called memory integrity, uses VBS to run Kernel Mode Code Integrity (KMCI) inside the secure VBS environment instead of the main Windows kernel. This helps prevent attacks that attempt to modify kernel mode code such as drivers. The KMCI role is to check that all kernel code is properly signed and hasn’t been tampered with before it is allowed to run.
HVCI ensures that only validated code can be executed in kernel-mode. The hypervisor leverages processor virtualization extensions to enforce memory protections that prevent kernel-mode software from executing code that has not been first validated by the code integrity subsystem. HVCI protects against common attacks like WannaCry that rely on the ability to inject malicious code into the kernel. HVCI can prevent injection of malicious kernel-mode code even when drivers and other kernel-mode software have bugs.
All Windows 11 devices will support HVCI and most new devices will come with VBS and HVCI protection turned on by default.
Windows 11 Secured-core PCs
The March 2021 Security Signals report shows that more than 80% of enterprises have experienced at least one firmware attack in the past two years. For customers in data sensitive industries like financial services, government, and healthcare, Microsoft has worked with OEM partners to offer a special category of devices called Secured-core PCs. The devices ship with additional security measures enabled at the firmware layer, or device core, that underpins Windows.
Secured-core PCs strengthen protection against advanced threats such as kernel attacks from ransomware. Secured-core PCs help prevent malware attacks and minimize firmware vulnerabilities by launching into a clean and trusted state at startup, with a hardware-enforced root of trust, stopping infections in their tracks. Virtualization-based security comes enabled by default. And with built-in hypervisor-protected code integrity that protects system memory, Secured-core PCs ensure that all operating system code is trustworthy, and executables are signed by known and approved authorities only.
Benefits of a Secured-core Windows 11 PC include:
- Powerful security capabilities integrated across software, hardware, firmware,and identity protection
- Deep integration between Microsoft, device manufacturers, and chip manufacturers to deliver powerful security capabilities that help prevent infections across software, firmware, and hardware
- Security features across the stack are enabled by default by device manufacturers helping ensure customers are secure from the start
Memory protection in Secured-core PCs
PCIe hotplug devices such as Thunderbolt, USB4, and CFexpress allow users to attach new classes of external peripherals, including graphics cards or other PCI devices, to their PCs with an experience identical to USB. Because PCI hotplug ports are external and easily accessible, PCs are susceptible to drive-by Direct Memory Access (DMA) attacks. Memory access protection (also known as Kernel DMA Protection) protects PCs against drive-by DMA attacks that use PCIe hotplug devices by limiting these external peripherals from being able
to directly copy memory when the user has locked their PC.
Drive-by DMA attacks typically happen quickly while the system owner isn’t present. The attacks are performed with simple to moderate attacking tools created with affordable, off-the-shelf hardware and software that do not require the disassembly of the PC. For example, a PC owner might leave a device for a quick coffee break. Meanwhile, an attacker plugs in a USB-like device and walks away with all the secrets on the machine or injects malware that gives the attacker full remote control over the PC, including the ability to bypass the lock screen.
Note, Memory access protection does not protect against DMA attacks via older ports like 1394/FireWire, PCMCIA, CardBus, or ExpressCard.Learn how to check if your PC supports Kernel DMA protection and about Kernel DMA protection requirements.
Firmware protection in Secured-core PCs
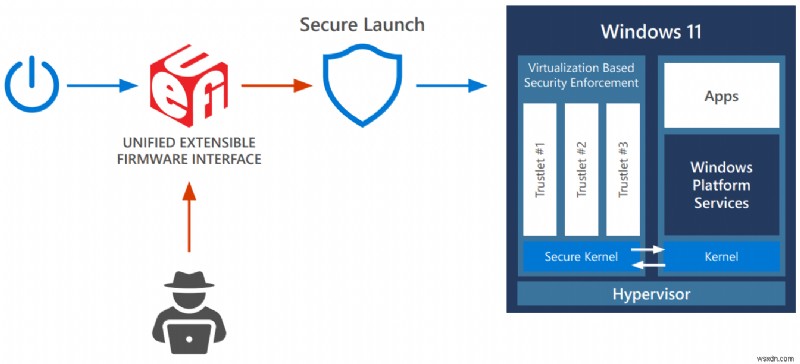
Secured-core PCs defend at the firmware level with multiple layers of protection enabled, helping ensure that devices launch safely in a hardware-controlled state.
Sophisticated malware attacks may commonly attempt to install “bootkits” or “rootkits” on the system to evade detection and achieve persistence. This malicious software may run at the firmware level prior to Windows being loaded, or during the Windows boot process itself, enabling the system to start with the highest level of privilege. Because critical subsystems in Windows leverage virtualization-based security, protecting the hypervisor becomes increasingly important. To ensure that no unauthorized firmware or software can start before the Windows bootloader, Windows PCs rely on the Unified Extensible Firmware Interface (UEFI) Secure Boot standard. The secure boot helps ensure that only authorized firmware and software with trusted digital signatures can execute. In addition, measurements of all boot components are securely stored in the TPM to help establish a non-repudiable audit log of the boot called the Static Root of Trust for Measurement (SRTM).
With thousands of PC vendors producing numerous PC models with diverse UEFI firmware components, there becomes an incredibly large number of SRTM signatures and measurements at bootup that are inherently trusted by secure boot, making it more challenging to constrain trust on any particular device to only what is needed to boot that device. Two techniques exist to constrain trust:either maintain a list of known “bad” SRTM measurements, also called a block list, which suffers from the drawback of being inherently brittle; or maintain a list of known “good” SRTM measurements, or an allow list, which is difficult to keep up-to-date at scale.
In Secured-core PCs, Windows Defender System Guard Secure Launch addresses these issues with a technology known as the Dynamic Root of Trust for Measurement (DRTM). DRTM lets the system follow the normal UEFI Secure Boot process initially, but before Windows is launched the system enters a hardware-controlled trusted state that forces the CPU(s) down hardware secured code path. If a malware rootkit/bootkit bypassed UEFI Secure Boot and had been resident in memory, DRTM will prevent it from accessing secrets and critical code protected by the virtualization-based security environment. System Management Mode (SMM) isolation complements the protections provided by DRTM by helping to reduce the attack surface from SMM, which is an execution mode in x86-based processors that runs at a higher effective privilege than the hypervisor. Relying on capabilities provided by silicon providers like Intel and AMD, SMM isolation enforces policies that enforce restrictions such as preventing SMM code from accessing OS memory. The SMM isolation policy in effect on a system can also be reliably provided to a remote attestation service. 8
Operating System Security
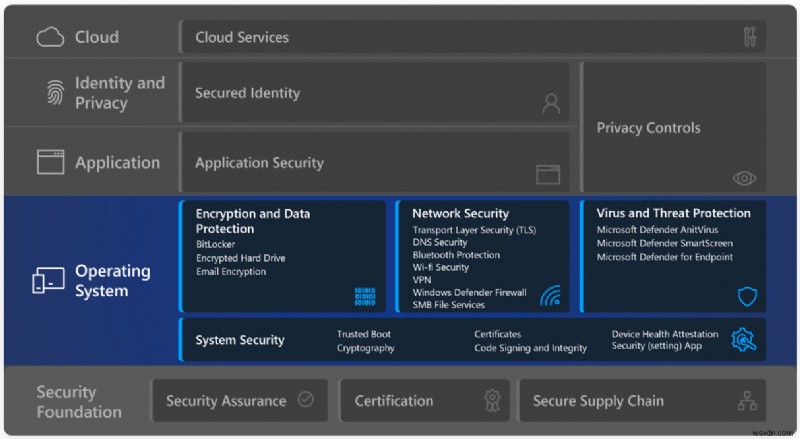
Hardware-based protection is only one link in the chain of chip to cloud security. Security and privacy also depend on an OS that guards your information and PC from when it starts.
Windows 11 is the most secure Windows yet with extensive security measures in the OS designed to help keep you safe. These measures include built-in advanced encryption and data protection, robust network and system security, and intelligent safeguards against ever-evolving viruses and threats. Windows 11 enhances built-in hardware protection with OS security out-of-the-box to help keep your plan, identity, and information safe.
System security
Trusted Boot (UEFI Secure Boot + Measured Boot)
The first step in protecting the operating system is to ensure that it boots securely after the initial hardware and firmware boot sequences have safely finished their early boot sequences. Secure Boot makes a safe and trusted path from the Unified Extensible Firmware Interface (UEFI) through the Windows kernel’s Trusted Boot sequence. Malware attacks on the Windows boot sequence are blocked by the signature-enforcement handshakes throughout the boot sequence between the UEFI, bootloader, kernel, and application environments.
As the PC begins the boot process, it will first verify that the firmware is digitally signed, reducing the risk of firmware rootkits. Secure Boot then checks all code that runs before the operating system and checks the OS bootloader’s digital signature to ensure that it is trusted by the Secure Boot policy and hasn’t been tampered with.
Trusted Boot takes over where Secure Boot leaves off. The Windows bootloader verifies the digital signature of the Windows kernel before loading it. The Windows kernel, in turn, verifies every other component of the Windows startup process, including boot drivers, startup files, and your antimalware product’s early-launch antimalware (ELAM) driver. If any of these files have been tampered with, the bootloader detects the problem and refuses to load the corrupted component. Tampering or malware attacks on the Windows boot sequence are blocked by the signature-enforcement handshakes between the UEFI, bootloader, kernel, and application environments.
Often, Windows can automatically repair the corrupted component, restoring the integrity of Windows and allowing the PC to start normally.
For more information about these features and how they help prevent rootkits and boot kits from loading during the startup process, see Secure the Windows boot process.
Windows 11 requires all PCs to use Unified Extensible Firmware Interface (UEFI)’s Secure Boot feature.
Cryptography
Cryptography is a mathematical process to protect the user and system data, by, for example, encrypting data so that only a specific recipient can read it by using a key possessed only by that recipient. Cryptography is a basis for privacy to prevent anyone except the intended recipient from reading data, provides integrity checks to ensure data is free of tampering, and authentication that verifies identity to ensure that communication is secure. The cryptography stack in Windows extends from the chip to the cloud enabling Windows, applications, and services to protect system and user secrets.
Cryptography on Windows 11 is subject to Federal Information Processing Standards (FIPS) 140 certification. FIPS 140 certification ensures that US government approved algorithms are correctly implemented (which includes RSA for signing, ECDH with NIST curves for key agreement, AES for symmetric encryption, and SHA2 for hashing), tests module integrity to prove that no tampering has occurred and proves the randomness for entropy sources.
Windows cryptographic modules provide low-level primitives such as:
- Random number generators (RNG)
- Support for AES 128/256 with XTS, ECB, CBC, CFB, CCM, GCM modes of operation; RSA and DSA 2048, 3072, and 4096 key sizes; ECDSA over curves P-256, P-384, P-521
- Hashing (support for SHA1, SHA-256, SHA-384, and SHA-512)
- Signing and verification (padding support for OAEP, PSS, PKCS1)
- Key agreement and key derivation (support for ECDH over NIST-standard prime curves P-256, P-384, P-521 and HKDF)
These are natively exposed on Windows through the Crypto API (CAPI) and the Cryptography Next Generation API (CNG) which is powered by Microsoft’s open-source cryptographic library SymCrypt. Application developers can leverage these APIs to perform low-level cryptographic operations (BCrypt), key storage operations (NCrypt), protect static data (DPAPI), and securely share secrets (DPAPI-NG).
Certificates
Windows offers several APIs to operate and manage certificates. Certificates are crucial to public key infrastructure (PKI) as they provide the means for safeguarding and authenticating information. Certificates are electronic documents, which conform to the X.509v3 formatting standard, used to claim ownership of a public key. Public keys are used to prove server and client identity, validate code integrity, and used in secure emails. Windows offers users the ability to auto-enroll and renew certificates in Active Directory with Group Policy to reduce the risk of potential outages due to certificate expiration or misconfiguration. Windows validates certificates through an automatic update mechanism that downloads certificate trust lists (CTL) weekly. Trusted root certificates are used by applications as a reference for trustworthy PKI hierarchies and digital certificates. The list of trusted and untrusted certificates is stored in the CTL and can be updated by the Microsoft Third-Party Root Program. Roots in the Microsoft Third-Party Root Program are governed through annual audits to ensure compliance with industry standards. For certificate revocation, a certificate is added as an untrusted certificate to the disallowed CTL that is downloaded daily causing the untrusted certificate to be revoked globally across user devices immediately.
Windows also offer enterprise certificate pinning to help reduce man-in-the-middle attacks by enabling users to protect their internal domain names from chaining to unwanted certificates. A web application’s server authentication certificate chain is checked to ensure it matches a restricted set of certificates. Any web application triggering a name mismatch will start event logging and prevent user access from Microsoft Edge or Internet Explorer.
Code signing and integrity
Code signing, while not a security feature by itself, is integral to establishing the integrity of firmware, drivers, and software across the Windows platform. Code signing creates a digital signature by encrypting the hash of the file with the private key portion of a code signing certificate and embedding the signature into the file. This ensures that the file hasn’t been tampered with, the Windows code integrity process verifies the signed file by decrypting the signature to check the integrity of the file and confirm that it is from a reputable publisher.
All software written and published by Microsoft is code-signed to establish that Windows and Microsoft code has integrity, authenticity, and a positive reputation. Code signing is how Windows can differentiate its own code from external creators and prevents tampering when code is delivered to user devices.
The digital signature is evaluated across the Windows environment on Windows boot code, Windows kernel code, and Windows user-mode applications. Secure Boot and Code Integrity verify the signature on bootloaders, Options ROMs, and other boot components, to ensure that it is trusted and from reputable publishers. For drivers not produced by Microsoft, external Kernel Code Integrity verifies the signature on kernel drivers and requires that drivers be signed by Windows or certified by the Windows Hardware Compatibility Program (WHCP). This program tests externally produced drivers for hardware and Windows compatibility and ensures that they are malware-free. Lastly, user-mode code, applications, Appx/MSIX packaged apps, Windows OS component updates, driver install packages, and their signatures, are evaluated by WinVerifyTrust which relies on the Crypto API. These signatures are verified by confirming they are in the Microsoft Third-Party Root Program CTL, and thus trusted and not revoked by the certificate authority.
Device health attestation
Device health attestation and conditional access are used to grant access to corporate resources. This helps reinforce a Zero Trust paradigm that moves enterprise defenses from the static, network- based perimeters to focus on users, assets, and resources.
Conditional access evaluates identity signals to confirm that users are who they say they are before they are granted access to corporate resources. Windows 11 supports remote attestation to help confirm that devices are in a good state and have not been tampered with. This helps users access corporate resources whether they’re in the office, at home, or when they’re traveling.
Information about the firmware, boot process, and software, which is cryptographically stored in the security co-processor (TPM), is used to validate the security state of the device. Attestation provides assurance of trust as it can verify the identity and status of essential components and that the device, firmware, and boot process have not been altered. This capability helps organizations to manage access with confidence. Once the device is attested it can be granted access to resources.
Device health attestation determines:
- If the device can be trusted. This is determined with the help of a secure root-of-trust, or TPM. Devices can attest that the TPM is enabled and in the attestation flow.
- If the OS booted correctly. Many security risks can emerge during the boot process as this can be the most privileged component of the whole system.
- If the OS has the right set of security features enabled.
Windows includes many security features to help protect users from malware and attacks. However, security components are trustworthy only if the platform boots as expected and was not tampered with. As noted above, Windows relies on Unified Extensible Firmware Interface (UEFI) Secure Boot, ELAM, DRTM, Trusted Boot, and other low-level hardware and firmware security features to protect your PC from attacks. From the moment you power on your PC until your anti-malware starts, Windows is backed with the appropriate hardware configurations that help keep you safe. Measured and Trusted boot, implemented by bootloaders and BIOS, verifies and cryptographically records each step of the boot in a chained manner. These events are bound to the TPM that functions as a hardware root of trust. Remote attestation is the mechanism by which these events are read and verified by a service to provide a verifiable, unbiased, and tamper resilient report. Remote attestation is the trusted auditor of your system’s boot, allowing relying parties to bind trust to the device and its security. As an example, Microsoft Intune integrates with Microsoft Azure Attestation to review Windows device health comprehensively and connect this information with AAD conditional access. This integration is key for Zero Trust solutions that help bind trust to an untrusted device.
A summary of the steps involved in attestation and Zero Trust on the Windows device are as follows:
- During each step of the boot process, such as a file load, update of special variables, and more, information such as file hashes and signatures are measured in the TPM Platform Configuration Register (PCRs). The measurements are bound by a Trusted Computing Group specification that dictates what events can be recorded and the format of each event.
- Once Windows has booted, the attestor (or verifier) requests the TPM to get the measurements stored in its PCRs alongside the measured boot log. Together these form the attestation evidence that’s sent to the Microsoft Azure Attestation Service.
- The TPM is verified by using the keys/cryptographic material available on the chipset with an Azure Certificate Service.
- The above information is sent to the Azure Attestation service to verify that the device is safe.
Microsoft Intune integrates with Microsoft Azure Attestation to review Windows device health comprehensively and connect this information with AAD conditional access – see Microsoft Azure Attestation Service section. This integration is key for Zero Trust solutions that help bind trust to an untrusted device.
Windows security policy settings and auditing
Security policy settings are a critical part of your overall security strategy. Windows provides a robust set of security setting policies that IT administrators can use to help protect Windows devices and other resources in your organization. Security settings policies are rules that you can configure on a device, or multiple devices, to control:
- User authentication to a network or device.
- Resources that users are permitted to access.
- Whether to record a user’s or group’s actions in the event log.
- Membership in a group.
Security auditing is one of the most powerful tools that you can use to maintain the integrity of your network and assets. Auditing can help identify attacks, network vulnerabilities, and attacks against targets that you consider high value. Auditing can help identify attacks, network vulnerabilities, and attacks against targets that you consider high value. You can specify categories of security-related events to create an audit policy tailored to the needs of your organization.
All auditing categories are disabled when Windows is first installed. Before enabling them, follow these steps to create an effective security auditing policy:
- Identify your most critical resources and activities.
- Identify the audit settings you need to track them.
- Assess the advantages and potential costs associated with each resource or setting.
- Test these settings to validate your choices.
- Develop plans for deploying and managing your audit policy.
Windows security app
Visibility and awareness of device security and health is key to any action taken. The Windows built-in security application found in settings provides an at-a-glance view of the security status and health of your device. These insights help you identify issues and take action to make sure you’re protected. You can quickly see the status of your virus and threat protection, firewall and network security, device security controls, and more.

Learn more about the Windows security app.
Encryption and data protection
When people travel with their PCs, their confidential information travels with them. Wherever confidential data is stored, it must be protected against unauthorized access, whether through physical device theft or from malicious applications.
BitLocker
BitLocker Drive Encryption is a data protection feature that integrates with the operating system and addresses the threats of data theft or exposure from lost, stolen, or inappropriately decommissioned computers. BitLocker uses AES algorithm in XTS or CBC mode of operation with 128-bit or 256-bit key length to encrypt data on the volume. Cloud storage on Microsoft OneDrive or Azure6 can be used to save recovery key content. BitLocker can be managed by any MDM solution such as Microsoft Intune6 using a configuration service provider (CSP).
BitLocker provides encryption for the OS, fixed data, and removable data drives leveraging technologies like hardware security test interface (HSTI), Modern Standby, UEFI Secure Boot and TPM. Windows consistently improves data protection by improving existing options and providing new strategies.
Encrypted hard drive
Encrypted Hard Drive uses the rapid encryption provided by BitLocker Drive Encryption to enhance data security and management.
By offloading the cryptographic operations to hardware, encrypted hard drives increase BitLocker performance and reduce CPU usage and power consumption. Because encrypted hard drives encrypt data quickly, BitLocker deployment can be expanded across enterprise devices with little to no impact on productivity.
Encrypted hard drives provide:
- Better performance:Encryption hardware, integrated into the drive controller, allows the drive to operate at full data rate with no performance degradation.
- Strong security based in hardware:Encryption is always “on” and the keys for encryption never leave the hard drive. User authentication is performed by the drive before it will unlock, independently of the operating system.
- Ease of use:Encryption is transparent to the user, and the user does not need to enable it. Encrypted hard drives are easily erased using on-board encryption key; there is no need to re-encrypt data on the drive.
- Lower cost of ownership:There is no need for new infrastructure to manage encryption keys, since BitLocker leverages your existing infrastructure to store recovery information. Your device operates more efficiently because processor cycles do not need to be used forthe encryption process.
Encrypted hard drives are a new class of hard drives that are self-encrypted at a hardware level and allow for full disk hardware encryption.
Email encryption
Email encryption (also referred to as Windows S/MIME), enables users to encrypt outgoing email messages and attachments, so only intended recipients with digital identification (ID)—also called a certificate—can read them. Users can digitally sign a message, which verifies the identity of the sender and ensures the message has not been tampered with. These encrypted messages can be sent by a user to people within their organization as well as external contacts if they have their encryption certificates. However, recipients using Windows 10 Mail app can only read encrypted messages if the message is received on their Exchange account and they have corresponding decryption keys.
Encrypted messages can be read-only by recipients who have a certificate. If an encrypted message is sent to recipient(s) whose encryption certificates are not available, the app will prompt you to remove these recipients before sending the email.
Learn more about configuring S/MIME for Windows.
Network security
Windows 11 raises the bar for networking security by bringing a wide array of improvements, helping people work, learn, and play from almost anywhere with confidence. New DNS and TLS protocol versions strengthen the end-to-end protections needed for applications, web services, and Zero Trust networking. File access adds an untrusted network scenario with SMB over QUIC as well as new encryption and signing capabilities. Wi-Fi and Bluetooth advancements provide greater trust in connections to other devices. The VPN and Windows Defender Firewall platforms bring new ways to configure easily and debug quickly, ensuring IT administrators and third-party software are more effective.
Transport layer security (TLS)
Transport Layer Security (TLS) is the internet’s most deployed security protocol, encrypting data to provide a secure communication channel between two endpoints. Windows prefers the latest protocol versions and strong cipher suites by default and offers a full suite of extension applications such as client authentication for enhanced server security, or session resumption for improved application performance.
TLS 1.3 is the latest version of the protocol and is enabled by default in Windows 11. This version eliminates obsolete cryptographic algorithms, enhances security over older versions, and aims to encrypt as much of the handshake as possible. The handshake is more performant with one fewer round trip per connection on average and supports only five strong cipher suites which provide perfect forward secrecy and less operational risk. Customers using TLS 1.3 (or Windows components that support it, including HTTP.SYS, WinInet, .NET, MsQUIC, and more) on Windows 11 will get more privacy and lower latencies for their encrypted online connections. Note that if the client or server application on either side of the connection does not support TLS 1.3, Windows will fall back to TLS 1.2.
DNS security
In Windows 11, the Windows DNS client supports DNS over HTTPS, an encrypted DNS protocol. This allows administrators to ensure their devices protect their name queries from on-path attackers, whether they are passive observers logging browsing behavior or active attackers trying to redirect clients to malicious sites. In a Zero Trust model where there is no trust placed in a network boundary, having a secure connection to a trusted name resolver is required.
Windows 11 provides Group Policy as well as programmatic controls to configure DNS over HTTP behavior. As a result, IT administrators can extent existing security models to adopt new security models such as Zero Trust. DNS over HTTP protocol can be mandated, ensuring that devices that use insecure DNS will fail to connect to network resources. IT administrators also have the option not to use DNS over HTTP for legacy deployments where network edge appliances are trusted to inspect plain-text DNS traffic. By default, Windows 11 will defer to the local administrator on which resolvers should use DNS over HTTP.
Support for DNS encryption integrates with existing Windows DNS configurations such as the Name Resolution Policy Table (NRPT), the system HOSTS file, as well as resolvers specified per network adapter or network profile. The integration helps Windows 11 ensure that the benefits of greater DNS security do not regress existing DNS control mechanisms.
Bluetooth protection
The number of Bluetooth devices connected to Windows continues to increase. Windows users connect their Bluetooth headsets, mice, keyboard, and other accessories and
improve their day-to-day PC experience by enjoying streaming, productivity, and gaming. Windows supports all standard Bluetooth pairing protocols, including classic and LE Secure connections, secure simple pairing, and classic and LE legacy pairing. Windows also implement host-based LE privacy. Windows updates help users stay current with OS and driver security features in accordance with the Bluetooth Special Interest Group (SIG) Standard Vulnerability Reports, as well as issues beyond those required by the Bluetooth core industry standards. Microsoft strongly recommends that you also ensure the firmware and/or software of your Bluetooth accessories are kept up to date.
IT-managed environments have a number of Bluetooth policies (MDM, Group Policy, and PowerShell) that can be managed through MDM tools such as Microsoft Intune. You can
configure Windows to use Bluetooth technology while supporting the security needs of your organization. For example, you can allow input and audio while blocking file transfer, force encryption standards, limit Windows discoverability, or even disable Bluetooth entirely for the most sensitive environments.
Securing Wi-Fi connections
Windows Wi-Fi supports industry standardized authentication and encryption methods when connecting to Wi-Fi networks. WPA (Wi-Fi Protected Access) is a security standard developed by the Wi-Fi Alliance to provide sophisticated data encryption and better user authentication. The current security standard for Wi-Fi Authentication is WPA3 which provides a more secure and reliable connection method and replaces WPA2 and the older security protocols. Opportunistic Wireless Encryption (OWE) is a technology that allows wireless devices to establish encrypted connections to public Wi-Fi hotspots.
WPA3 is supported in Windows 11 (WPA3 Personal and WPA3 Enterprise 192-bit Suite B) as well as OWE implementation for more security while connecting to Wi-Fi hotspots.
Windows 11 enhances Wi-Fi security by enabling additional elements of WPA3 security such as the new H2E protocol and WPA3 Enterprise Support which includes enhanced Server Cert validation and the TLS1.3 for authentication using EAP-TLS Authentication. Windows 11 provides Microsoft partners the ability to bring the best platform security on new devices.
WPA3 is now a mandatory requirement by WFA for any Wi-Fi Certification.
Windows defender firewall
Windows Defender Firewall with Advanced Security is an important part of a layered security model. It provides host-based, two-way network traffic filtering, blocking unauthorized traffic flowing into or out of the local device based on the types of networks to which the device is connected.
Windows Defender Firewall in Windows 11 offers the following benefits:
- Reduces the risk of network security threats:Windows Defender Firewall reduces the attack surface of a device with rules to restrict or allow traffic by many properties such as IP addresses, ports, or program paths. Reducing the attack surface of a device increases manageability and decreases the likelihood of a successful attack.
- Safeguards sensitive data and intellectual property:With its integration with Internet Protocol Security (IPsec), Windows Defender Firewall provides a simple way to enforce authenticated, end-to-end network communications. It provides scalable, tiered access to trusted network resources, helping to enforce the integrity of the data, and optionally helping to protect the confidentiality of the data.
- Extends the value of existing investments:Because Windows Defender Firewall is a host-based firewall that is included with the operating system, there is no additional hardware or software required. Windows Defender Firewall is also designed to complement existing non-Microsoft network security solutions through a documented application programming interface (API).
Windows 11 makes the Windows Defender Firewall easier to analyze and debug. IPsec behavior has been integrated with Packet Monitor (pktmon), an in-box cross-component
network diagnostic tool for Windows. Additionally, the Windows Defender Firewall event logs have been enhanced to ensure an audit can identify the specific filter that was responsible for any given event. This enables analysis of firewall behavior and rich packet capture without relying on third-party tools.
Virtual private networks (VPN)
Organizations have long relied on Windows to provide reliable, secured, and manageable virtual private network (VPN) solutions. The Windows VPN client platform includes built-in VPN protocols, configuration support, a common VPN user interface, and programming support for custom VPN protocols. VPN apps are available in the Microsoft Store for both enterprise and consumer VPNs, including apps for the most popular enterprise VPN gateways.
In Windows 11 we’ve integrated the most commonly used VPN controls right into the Windows 11 Quick Actions pane. From the Quick Actions pane, users can see the status of
their VPN, start and stop the VPN tunnels, and with one click can go to the modern Settings app for more control.
The Windows VPN platform connects to Azure Active Directory (Azure AD) and Conditional Access for single sign-on, including multi-factor authentication (MFA) through Azure AD. The VPN platform also supports classic domain-joined authentication. It’s supported by Microsoft Intune and other mobile device management (MDM) providers. The flexible VPN profile supports both built-in protocols and custom protocols, can configure multiple authentication methods, can be automatically started as needed or manually started by the end-user, and supports split-tunnel VPN and exclusive VPN with exceptions for trusted external sites.
With Universal Windows Platform (UWP) VPN apps, end users never get stuck on an old version of their VPN client. VPN apps from the store will be automatically updated as needed. Naturally, the updates are in the control of your IT admins.
The Windows VPN platform has been tuned and hardened for cloud-based VPN providers like Azure VPN. Features like AAD auth, Windows user interface integration, plumbing IKE traffic selectors, and server support are all built into the Windows VPN platform. The
integration into the Windows VPN platform leads to a simpler IT admin experience; user authentication is more consistent, and users can easily find and control their VPN.
SMB file services
SMB and file services are the most common Windows workload in the commercial and public sector ecosystem. Users and applications rely on SMB to access the files that run organizations large and small. In Windows 11, the SMB protocol has significant security updates to meet today’s threats, including AES-256 bits encryption, accelerated SMB signing, Remote Directory Memory Access (RDMA) network encryption, and an entirely new scenario, SMB over QUIC for untrusted networks.
SMB Encryption provides end-to-end encryption of SMB data and protects data from eavesdropping occurrences on internal networks. Windows 11 introduces AES-256-GCM and
AES-256-CCM cryptographic suites for SMB 3.1.1 encryption. Windows will automatically negotiate this more advanced cipher method when connecting to another computer that requires it and it can also be mandated on clients.
Windows 11 Enterprise, Education, and Pro Workstation SMB Direct now support encryption. For demanding workloads like video rendering, data science, or huge files, you can now operate with the same safety as traditional TCP and the performance of RDMA. Previously, enabling SMB encryption disabled direct data placement, making RDMA slow as TCP. Data is encrypted before order, leading to relatively minor performance degradation while adding AES-128 and AES-256 protected packet privacy.
Windows 11 introduces AES-128-GMAC for SMB signing. Windows will automatically negotiate this better-performing cipher method when connecting to another computer that
supports it. Signing prevents common attacks like a relay, spoofing, and is required by default when clients communicate with Active Directory domain controllers.
Finally, Windows 11 introduces SMB over QUIC (Preview), an alternative to the TCP network transport, providing secure, reliable connectivity to edge file servers over untrusted networks like the Internet and highly secure communications on internal networks. QUIC is an IETF-standardized protocol with many benefits compared to TCP, but most importantly, it always requires TLS 1.3 and encryption. SMB over QUIC offers an “SMB VPN” for telecommuters, mobile device users, and high-security organizations. All SMB traffic, including authentication and authorization within the tunnel, is never exposed to the underlying network. SMB behaves normally within the QUIC tunnel, meaning the user experience doesn’t change. SMB over QUIC will be a game-changing feature for Windows 11 accessing Windows file servers and eventually Azure Files and third parties.
Virus and threat protection
Today’s cyber threat landscape is more complex than ever. This new world requires new threat prevention, detection, and response approach. Microsoft Defender Antivirus, along with many other features built into Windows 11, are at the frontlines to protect customers against current and emerging threats.
Microsoft Defender Antivirus
Microsoft Defender Antivirus is a next-generation protection solution included in Windows 10 and Windows 11. Once you boot Windows, Microsoft Defender Antivirus continually monitors for malware, viruses, and security threats. In addition to this real-time protection, updates are downloaded automatically to help keep your device safe and protect it from threats. For example, if you have another antivirus app installed and turned on, Microsoft Defender Antivirus will turn off automatically. Likewise, if you uninstall the other app, Microsoft Defender Antivirus will turn back on.
Microsoft Defender Antivirus includes real-time, behavior-based, and heuristic antivirus protection. This combination of always-on content scanning, file and process behavior monitoring, and other heuristics prevents security threats. Microsoft Defender Antivirus continually scans for malware and threats. Also, it detects and blocks potentially unwanted applications (PUA), which are applications that are deemed to impact your device negatively but are not considered malware. Microsoft Defender Antivirus always-on on device prevention is integrated with cloud-delivered protection, which helps ensures near-instant detection and blocking of new and emerging threats. 9
Attack surface reduction
Available in Windows and Windows Server, attack surface reduction rules help prevent software behaviors that are often abused to compromise your device or network. By reducing the number of attack surfaces, you can reduce the overall vulnerability of your organization. In addition, administrators can configure specific attack surface reduction rules to help block certain behaviors, such as:
- Launching executable files and scripts that attempt to download or run files
- Running obfuscated or otherwise suspicious scripts
- Performing behaviors that apps don’t usually initiate during normal day-to-day work
For example, an attacker might try to run an unsigned script from a USB drive or have a macro in an Office document make calls directly to the Win32 API. Attack surface reduction rules can constrain these kinds of risky behaviors and improve the defensive posture of the device.
For comprehensive protection, follow steps to enable hardware-based isolation for Microsoft Edge and reduce the attack surface across applications, folders, devices, networks, and firewalls.
Lean more about attack surface reduction.
Tamper Protection
Attacks like ransomware attempt to disable security features on targeted devices, such as anti-virus protection. Bad actors like to disable security features to get easier access to users’ data, install malware, or otherwise exploit users’ data, identity, and devices without fear of being blocked. Tamper protection helps prevent these kinds of activities.
With tamper protection, malware is prevented from taking actions such as:
- Disabling virus and threat protection
- Disabling real-time protection
- Turning off behavior monitoring
- Disabling antivirus (such as IOfficeAntivirus (IOAV))
- Disabling cloud-delivered protection
- Removing security intelligence updates
Learn more about tamper protection.
Network Protection
Network protection in Windows helps prevent users from accessing dangerous IP addresses and domains that may host phishing scams, exploits, and other malicious content on the Internet. Network protection is part of attack surface reduction and helps provide an additional layer of protection for a user. Using reputation-based services, network protection blocks access to potentially harmful, low-reputation-based domains and IP addresses. Network protection works best with Microsoft Defender for Endpoint in enterprise environments, which provides detailed reporting into protection events as part of more significant investigation scenarios.
Learn more about how to protect your network.
Controlled Folder Access
You can protect your valuable information in specific folders by managing app access to specific folders. Only trusted apps can access protected folders, specified when controlled folder access is configured. Typically, commonly used folders, such as those used for documents, pictures, and downloads, are included in the list of controlled folders.
Controlled folder access works with a list of trusted apps. Apps that are included in the list of trusted software work as expected. Apps that are not included in the trusted list are prevented from making any changes to files inside protected folders.
Controlled folder access helps protect users’ valuable data from malicious apps and threats, such as ransomware. Learn more about controlled folder access.
Exploit protection
Exploit protection automatically applies several exploit mitigation techniques to operating system processes and apps. Exploit protection works best with Microsoft Defender for Endpoint, which gives organizations detailed reporting into exploit protection events and blocks as part of typical alert investigation scenarios. In addition, you can enable exploit protection on an individual device and then use Group Policy to distribute the XML file to multiple devices simultaneously.
When mitigation is encountered on the device, a notification will be displayed from the Action Center. You can customize the message with your company details and contact information. You can also enable the rules individually to customize which techniques feature monitors.
You can use audit mode to evaluate how to exploit protection would impact your organization if it were enabled.
Windows 11 provides configuration options for exploit protection. You can prevent users from modifying these specific options with Group Policy.
Learn more about protecting devices from exploits.
Microsoft Defender SmartScreen
Microsoft Defender SmartScreen protects against phishing, malware websites and applications, and the downloading of potentially malicious files.
SmartScreen determines whether a site is potentially malicious by:
- Analyzing visited web pages looking for indications of suspicious behavior. If a page is suspicious, it will show a warning page to advise caution.
- Checking the visited sites against a dynamic list of reported phishing sites and malicious software sites. If it finds a match, Microsoft Defender SmartScreen shows a warning to let users know that the site might be malicious.
SmartScreen also determines whether a downloaded app or app installer is potentially malicious by:
- Checking downloaded files against a list of reported malicious software sites and programs known to be unsafe. SmartScreen warns the user that the site might be malicious if it finds a match.
- Checking downloaded files against a list of well-known and downloaded files by many Windows users. If the file is not on that list, it shows a warning advising caution.
The app and browser control section contains information and settings for Windows Defender SmartScreen. IT administrators and IT pros can get configuration guidance in the Windows Defender SmartScreen documentation library.
Microsoft Defender for Endpoint
Windows E5 customers benefit from Microsoft Defender for Endpoint, an enterprise endpoint detection and response capability that helps enterprise security teams detect, investigate, and respond to advanced threats. Organizations with a dedicated security operations team can use the rich event data and attack insights that Defender for Endpoint provides to investigate incidents. In addition, a defender for Endpoint brings together the following elements to give a complete picture of security incidents:
- Endpoint behavioral sensors:Embedded in Windows, these sensors collect and process behavioral signals from the operating system and send this sensor data to your private, isolated, cloud instance of Microsoft Defender for Endpoint.
- Cloud security analytics:Leveraging big-data, device-learning, and unique Microsoft optics across the Windows ecosystem, enterprise cloud products such as Microsoft 365 and online assets, behavioral signals are translated into insights, detections, and recommended responses to advanced threats.
- Threat intelligence:Microsoft’s threat intelligence is informed daily by trillions of security signals. Combined with our global team of security experts, cutting-edge artificial intelligence, and machine learning, we can see threats that others miss. Our threat intelligence helps provide unparalleled protection for our customers.
Defender for Endpoint is also part of Microsoft 365 Defender, a unified pre- and post-breach enterprise defense suite that natively coordinates detection, prevention, investigation, and response across endpoints, identities, email, and applications to provide integrated protection against sophisticated attacks.
Learn more about Microsoft Defender for Endpoint and Microsoft 365 Defender.
© 2021 Microsoft Corporation. All rights reserved.
